Cyber Security in the Public Service
Episode 18
In this episode, you will:
- learn the definition of cyber security
- find out how adept you are at identifying scams
- hear about the cyber security challenges facing the Government of Canada (GC)
- learn 7 ways to protect the data you work with and your personal information
Your morning begins with your smartphone alarm ringing. You hit play on your favourite song, maybe Amy Winehouse’s “Valerie”, Elton John's "Bennie And The Jets" or some Bruno Mars "Blinding Lights" to help get you moving for the day ahead. You might drop off your kids to school on the way to work. You check the weather before switching between your Instagram feed, Spotify, Audible or Gmail to pass the time. You get to work and tuck your phone away, but keep it running to check it throughout the day. Like most Canadians, you’re likely using an Android or Apple device.
With your phone tucked away, you make a palpable switch to a Windows-based desktop or laptop and use either Internet Explorer as your browser or Google Chrome, if you’re allowed to. You store documents in GCdocs as you've been trained and you don’t publish secret government data. You’ve done the required internal online security training. You’re pretty confident you’re protecting the government’s data and believe it’s IT Security’s role to do that on a bigger scale.
Like everyone else, you’re at the epicentre of a network of private companies that have your personal data in common. You’re tangled in a service web in which each thread has unique legal properties and social ramifications. Unlike everyone else, however, you travel from this world to the idiosyncratic world of GC security five days a week.
What is cyber security?
The term cyber security is a relatively new one. In simple terms, cyber security is the act of protecting your data and the sensitive information that you store online, on a server, or in the cloud.
Data breaches, hacking, malware, ransomware, viruses, phishing—you can’t avoid hearing about nefarious actors. The online world has become a scary place and as a public servant, you will have been warned about the need for cyber security. And although you get it, you probably fall into one of three camps:
1. The Fatalist: High fear, low action
“It’s too late. Privacy is dead and I have nothing to hide, so I’ve given up trying to protect myself from threats. Yeah, it’s scary, but I really can’t do anything about it.”
2. The Fearmonger: High fear, high action

“‘Black Mirror’ is an accurate portrayal of what’s already happening. There are malevolent groups out there mining our data for profit and orchestrating personal attacks. Ordinary citizens like me are at real risk. We have to read the terms and conditions of every app we download, carefully manage privacy settings on every device, cover our cameras and assume everything we post, draft or say out loud can be used against us.”
3. The Hedonist: Low fear, low action
“Social media and apps have had a hugely positive impact on my life. I love being connected. The benefits of living digitally far outweigh the risks. People might occasionally get scammed, but banks and the government are looking out for us, so the risk is pretty low. Fake videos are made about prominent figures; I’m not rich or famous, so I’m not concerned.”
Which one are you? Tell us about it in the comments below.
Much like our favourite superheroes, we live double lives. When Peter Parker transforms into Spiderman, he doesn’t forget who he is as a person. It would be naive to think that our attitudes towards our own data don’t spill over into the way we look after work data.
If we’re apathetic hedonists in our own lives, what’s the likelihood we are leading the pack on securing GC data Monday morning?

Fear is a complex emotion; we’re biologically programmed to avoid things that cause it. When we read the news about massive data breaches, we “other” the experience, soothing ourselves with, “That’s the private sector, it can’t happen here” or “That’s that department; they weren’t as prepared as we are.” In other words, we lull ourselves into a false sense of security.
How often do cyber attacks happen?
In 2019, the World Economic Forum ranked cyber attacks as one of the top ten most likely global risks. While less likely than extreme weather conditions and natural disasters, they were on par with weapons of mass destruction for impact.
In addition, our clients, Canadian citizens, are increasingly worried about this issue. Edelman’s 2019 Trust Barometer showed that 71% of Canadians worried about false information or fake news being weaponized, an increase of 6% year over year.
My department or project is too small to be bothered with.
In 2017, a vulnerability was detected in the websites of the Canada Revenue Agency and Statistics Canada. In response, parts of the CRA website were shut down and certain Statistics Canada servers were taken offline. At the time, Statistics Canada had just over 5,000 staff, in contrast to the 40,000 at CRA, challenging the notion that large, influential companies and departments are hackers’ only prey. As public servants, we work with departmental and personal data and in research and development, which can be attractive to hackers and competitors. Email phishing campaigns have been tested on internal staff by Treasury Board Secretariat and Immigration, Refugees and Citizenship Canada to raise awareness and cyber security acumen. Register now for the February 19 CSPS cyber security event/webcast to learn more about how to protect GC data from threats.
We often focus on the financial impact of being hacked— the cost of new IT systems, new security software or hardware, and retribution to those who were harmed. However, it is the reputational damage resulting from a cyber attack that can cripple an organization and derail its modernization efforts.
Imagine what would happen if:
- the personal information Canadians entrust us with were lost or stolen
- your departmental website were hacked and had malicious malware embedded into it
- the Government of Canada were flooded with spam email that crashed the communication network
How would that make the government look? And what would be the cost to taxpayers?
7 steps you can take today
- Keep an eye out for suspicious emails: Can you spot a phishing scam? Many departments tell their employees not to open email from unfamiliar email addresses, even if the source appears to be reputable. Be wary of emails that: contain grammatical or spelling errors, address you by your last name, ask that you click on a link or make any kind of unusual request. When in doubt, send any suspicious email to your IT department to determine its legitimacy.
- Beef up your passwords: Picking better passwords can prevent many cyber crimes. A six-letter password is stronger than a four-letter password, and a 10-letter password is even better. Making your passwords a little more complex can make a difference.
- Maintain physical security of company and personal devices: Keep external doors and file server rooms locked, and refuse unauthorized entry to strangers. If a hacker can get into the building and sit down at a terminal, the job of breaking into a network is that much easier.
- Risk assessment: Understand what to protect. Take proactive steps to understand the threats your organization faces and prioritize your efforts by honing in on high/medium risks.
- Security awareness: Make sure that you and your team are fully trained. Having the latest technology to protect yourself is not enough when your biggest flaw could simply be poor password management or how your coworkers are storing data. Do they know what’s expected of them and what’s permitted? Start a conversation in the comments below.
- Build a strategy: Much like you would plan what to do in the event of a fire, plan what to do before, during and after a cyber attack. The strategy should complement business objectives and focus on continual improvement.
- Use safer software: Internet Explorer is the default browser for many, but there is evidence that it’s not the most secure option.

Let’s try to make it fun rather than frightening! Here are two games you can play to see how good you are at spotting the risk:
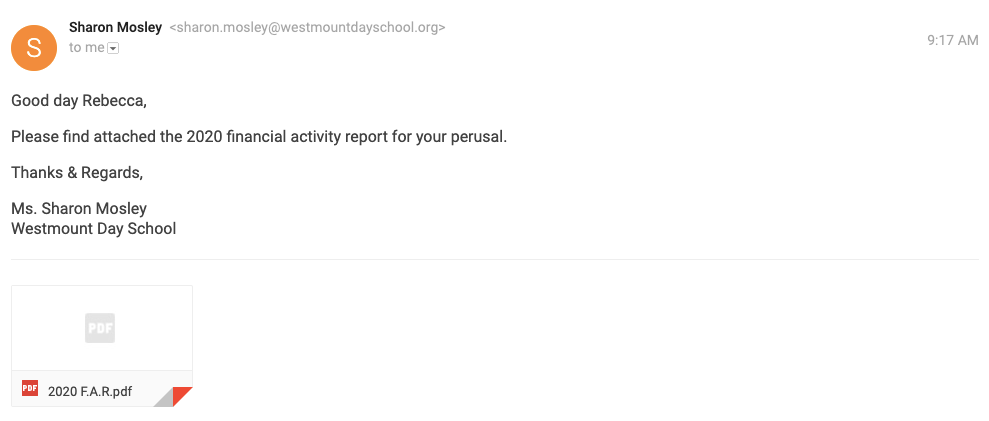
Can you tell if this is a phishing email? Take the Google Phishing Quiz to see how you fare. Let us know how you did in the comment section!
You’re the chief information officer of a global company that is about to release a new payment app. Steer the team through the final stages of the project in Targeted Attack: The Game.

Resources
- CSPS Event | February 19 | Strengthening Cyber Security in the Public Service Register here
- Targeted Attacks Game
- Google Phishing Quiz
- Canadian Internet Registration Authority | 2018 Cybersecurity Report
- Security Awareness Summit Deck | Using Gamification to Transform Security Awareness
- Globe and Mail | Experts warn Canadians to brace for a new era of cyberthreats